cyberbarf
EXAMINE THE NET WAY OF LIFE
Vol. 5 No. 7
February, 2006
|
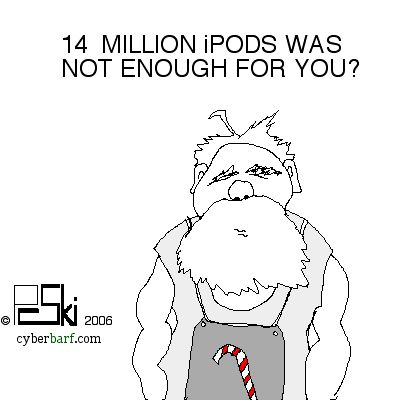
IN THIS ISSUE: iToon on 39 cents iPod, Therefore iAm iToon on Holiday Pods
Googlization iToon on Mr. Ed Pitch THE NEW WORLD
iToon on Modern Intellectualism The Meaningless Network iToon on Computer Blowout |
|
|
iToon
cyberbarf
EXAMINE THE NET WAY OF LIFE
iPod,
Therefore, iAm
When an old school blue jean manufacturer now includes a special pocket in its product, you know that the iPod has gone mainstream in a big way.
iPod,
Therefore, iAm
NEW T-SHIRT AT THE CYBERBARF STORE!
iToon
The software upgrade came on disc. Some of the older iMacs would not recognize the CD. Then it determined that the OS update came on a DVD and many of the older machines only had a CD-R. It appeared that one needed to have the disc on the machine drive in order to install.
Time to learn something new.
Connect a laptop with a DVD drive to the computer to be updated. Insert the upgrade OS DVD. Restart by holding down the T key. This turns the laptop into a Borg assimilation ship. The above icon begins to roam around the laptop screen. Then you restart the destination machine by holding down the ALT key and now the assimilation is complete. It is called Target Disk Mode. It gives an accessory drive the ability to become the start-up installer. The installation software appears on the iMac, and you click your way to an easy installation. It is like a stupid human trick, but it was a cool solution to a possible vexing situation. With automatic software updating features built in to most OS menus, the possibility of skipping a few updates is remote. Unless it is upgrading to a new (i.e. major) upgrade that the manufacturer wants new cash for each install.
So the Borg laptop went from work station to work station installing the new operating system discs. On only one occasion did the install disc stall and fail to complete its mission. (Just like a Star Trek cliffhanger episode.) Watching the Y-logo move slowly around the laptop screen had an erie quality; leaving the software to do all the work in secret. The installation was completed and the new system was installed with only one freeze incident on one desktop out of five.
Googlization
Word on the street is that GOOGLE is going to take over the world. It is just a matter of when.
The first evil empire in the new technology era was Microsoft. Bill Gates was going to control every aspect of the computer world through the mandatory use of his Windows operating system. It made him a multi-billionaire. Multiple generations of desktop business systems were trapped in the Windows world as it became the default standard.
The Internet has changed the landscape of business. Now the browser is replacing the individual operating system as the next standard. Alternatives to Microsoft's dominance have been slowly creeping into the picture. Enterprise software solutions are on par with the next Internet strategy.
The simple task of searching the Internet spawned two major companies, Yahoo and Google. The search engine is the Swiss Army knife for web surfers. It is a basic tool. Everyone knows how to use it. By habit, it is simple transparent exercise. The revenue side of the search engine company has always been advertising. The new form of ad circulation, the click view. But in order to meet the unrealistic Wall Street growth projections, search companies had to continue to squeeze the business model to increase revenue streams.
Google was on the leading edge of creating new ways to increase revenue in the simple search engine universe. It offered pay search databases targeting specialized business groups. It offered to sell companies prime listings for search engine result pages. The hope was more page views for web publishers, to increase traffic ad revenues. Now, it is offering affiliate advertising, placing its advertisers on individual web pages with revenue sharing.
Google is portrayed as the poster child for the next evil empire. Googlization will be a negative word. Competitors will curse its market power and hordes of cash to make acquisitions or put its stamp on everything. Google is now rumored to use its billions in market capital to acquire content providers, scan search every publication printed, produce cheap alternative computer systems, and push everything net-worthy through its portals. Gmail was to corral email through its pages. But all the expansion themes still deal with the core of its business: trying to get more eyes on their advertising links. Google is still pushing its advertising on us, under different guises. It is trying to standardize net advertising under its global banner.
Googlization. It's all still just about advertising.
When the broadcasting industry started, only advertising would support its programming. Television and radio is advertising driven business enterprises. If you have a popular show, the network will receive higher advertising dollars which are tied to number of viewers. If you have a popular show, you will be rewarded. The same is true in the New Media. If you have a popular web site or web utility (like a search engine), you will be rewarded. The only currency is viewers; the only open issue is how to count them so advertisers can correlate Internet ad expenses with customer sales.
Google began making money from “finding” designated web content through keywords and sorting software parameters. It moved into “controlling” search results by paid search rankings, paid banner ads on search pages, sponsored links, and affiliated click ads. It has begun to reach beyond its own page development to “taking ownership” over content by attempting to scan all books into a searchable database to the horror of copyright owners who have the exclusive right to authorize copies or views of their work (for a royalty).
Google needs to expand its revenue growth in order to keep its sky-high stock price in the outer atmosphere. Microsoft had the same huge growth margins during the last tech boom. Microsoft's stock created a huge cash cow for the leading operating system software firm. The company staked everything on the continued growth of Windows as the standard operating system for computers and next generation computer like devices, like cell phones, PDAs, ect. With billions in retained earnings, and the OS license revenue at a plateau, Microsoft attempted to leverage more growth by buying, taking or throwing cash at new ventures outside its core competency: hardware, game box developer, Internet browser king. But the marketplace placed road blocks against such expansion, either in quality or monopoly issues. The company was always behind the cutting edge independent developers to take away fickle end users. So Microsoft has had its stock turn into a tech utility, a narrow trading range and consistent business news. If Google throws its billions in markets beyond the search engine venue, it may wind up on the same plain vanilla shelf as Microsoft.
iToon